Security and Analytics
Elasticsearch's combination of fast full-text search, aggregation power, and horizontal scalability makes it a natural platform for security analytics. We build production-grade SIEM implementations on Elasticsearch — from raw log ingestion and normalization through to detection rules, automated alerting, and the Kibana dashboards your security operations team will actually use every day. Every pipeline we build is designed for the data volumes and query patterns of real security workloads.
Log Ingestion & Normalization
Security data arrives from dozens of sources — firewalls, cloud CloudTrail and Audit Logs, endpoint agents, WAFs, VPN gateways, and authentication services. Raw, unnormalized logs make correlation impossible. We build Logstash pipelines and Elastic Agent integrations that ingest all sources into a consistent structure based on the Elastic Common Schema (ECS), enriched with GeoIP lookups, threat intelligence feeds, and asset context from your CMDB.
-
Multi-source Logstash pipeline and Elastic Agent integration
-
ECS (Elastic Common Schema) field normalization
-
GeoIP, ASN, and threat intelligence enrichment
-
High-throughput ingest pipeline performance tuning

Detection Rules & Alerting
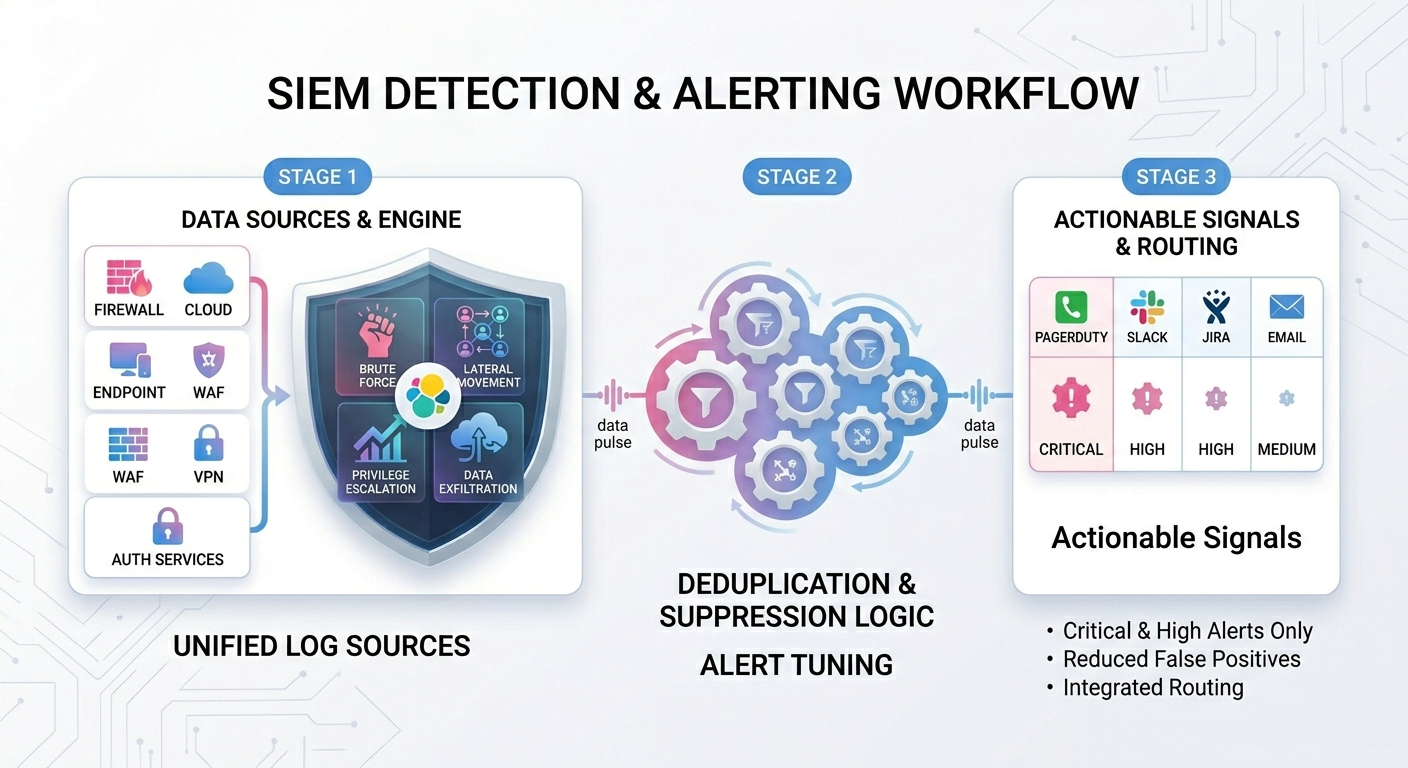
Detection is where SIEM implementations most often fall short — either generating so many false positives that analysts stop trusting alerts, or missing real threats due to poor rule design. We implement detection rules using Elasticsearch's SIEM detection engine and Watcher, tuned to your environment's baseline. Rules cover common attack patterns — brute force, lateral movement, privilege escalation, and data exfiltration — as well as business-specific scenarios identified during threat modeling workshops with your security team. Suppression and deduplication logic ensures analysts receive actionable signals, not a flood of repeated notifications. Alert routing integrates with PagerDuty, Slack, JIRA, or email depending on severity and team preference.
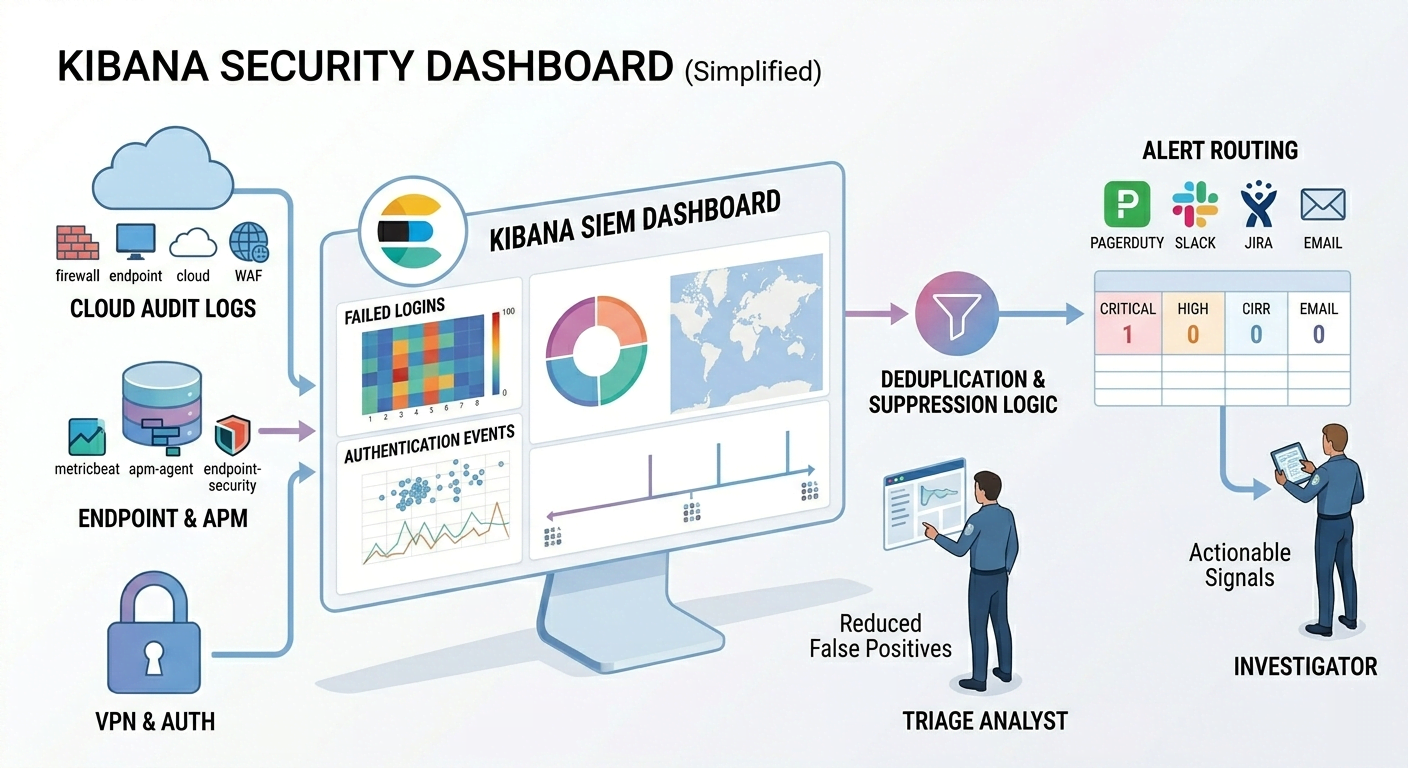
Kibana Security Dashboards
A SIEM is only useful if analysts can act on what they see. We build Kibana dashboards tailored to the workflows of your security operations center — authentication event timelines, failed login heatmaps, network traffic anomaly views, and executive-level risk summaries.
-
Role-based SOC dashboards — triage, investigation, and executive views
-
Authentication events, lateral movement, and exfiltration visualizations
-
Lens and TSVB visualization design with drill-down capability
-
Space- and role-based dashboard access control
-
Threat intelligence overlay with IOC feed integration
HOW CAN WE HELP?
CONTACT US
Search API Consultants
At Your Service
Providing tailored API solutions for clients to drive innovation, enhance scalability, and achieve success in the digital age. Let us help you unlock the full potential of your APIs.