Cluster Implementation & Management
An Elasticsearch cluster is not a commodity installation. The decisions made during provisioning — node roles, JVM settings, network configuration, storage layout, and security posture — compound into either a resilient production system or a fragile one that demands constant firefighting. We design, deploy, and hand over clusters that are built to handle real production traffic, survive hardware failures without data loss, and remain manageable as your team and data volumes grow.
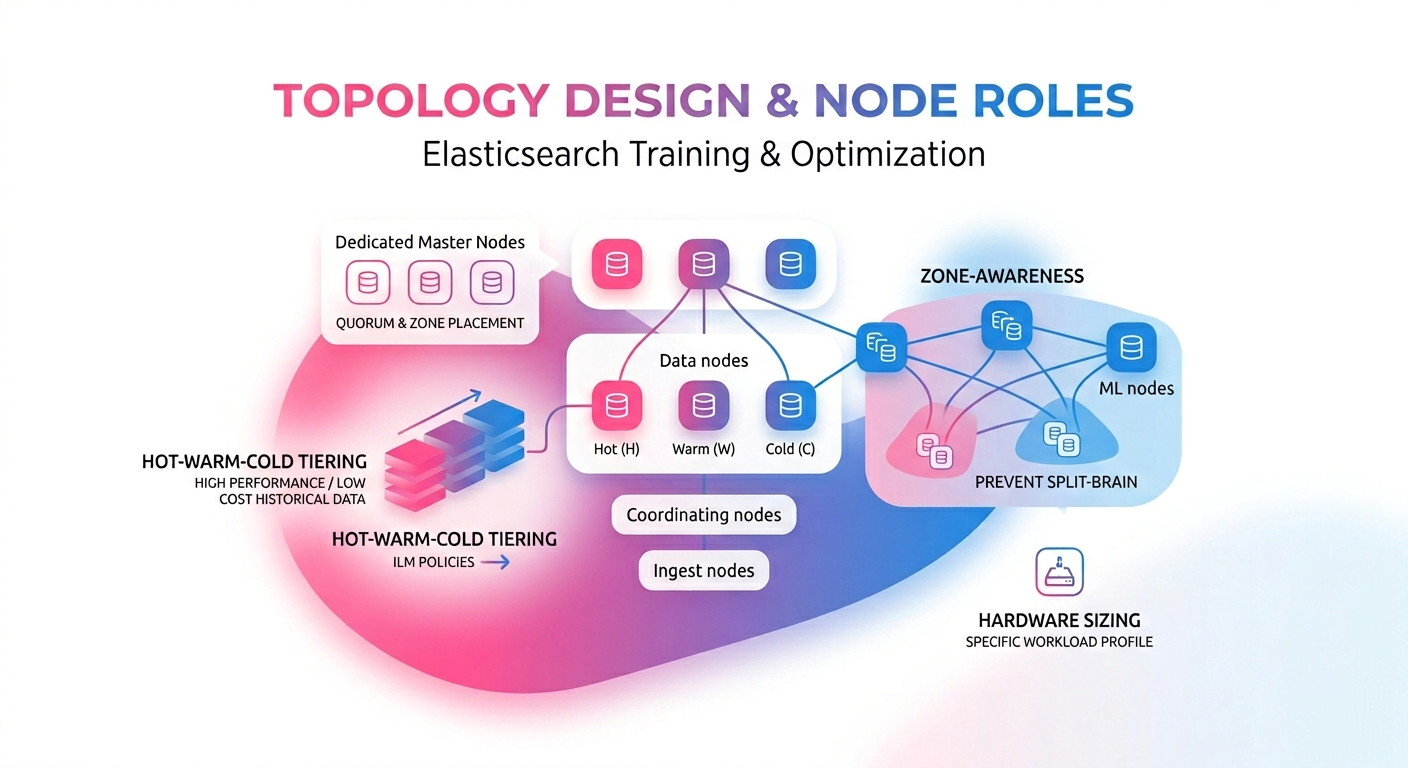
Topology Design & Node Roles
Mixing node roles on underpowered hardware is one of the most common causes of Elasticsearch instability. We design multi-node topologies where master, data, coordinating, ingest, and ML nodes are sized and separated appropriately for your query and indexing workload. For time-series and log-heavy use cases we implement hot-warm-cold tiering to keep query performance high while reducing storage cost on historical data. All deployments include zone-awareness configuration to prevent split-brain across availability zones.
-
Dedicated master node quorum sizing and zone placement
-
Hot-warm-cold data tier configuration and ILM policies
-
Cross-zone replica allocation and awareness attributes
-
Hardware sizing recommendations for your specific workload profile

Security, TLS & Access Control
An unsecured Elasticsearch cluster exposed to a network is a critical vulnerability. We configure the full security layer: TLS for transport and HTTP communication, X-Pack security with role-based access control, API key lifecycle management, and field- and document-level security where data segregation requirements demand it. Audit logging is configured to capture the events your compliance team needs without overwhelming your cluster with log volume.
-
TLS certificate provisioning, rotation, and auto-renewal
-
Role-based access control (RBAC) and API key management
-
Audit logging scoped to compliance requirements
Deployment Automation & IaC
Manually provisioned clusters are impossible to reproduce reliably and dangerous to modify. We deliver fully automated, version-controlled cluster deployments using the infrastructure-as-code tooling that fits your environment. On Kubernetes we use the Elastic Cloud on Kubernetes (ECK) operator with production-hardened Helm configurations. On cloud VMs or bare metal we use Terraform and Ansible. Every cluster definition lives in version control — meaning configuration changes go through review, rollback is a git revert, and provisioning a new environment is a single pipeline run. Snapshot repository configuration and automated snapshot scheduling are included in every deployment so your data is protected from the moment traffic hits the cluster.
HOW CAN WE HELP?
CONTACT US
Search API Consultants
At Your Service
Providing tailored API solutions for clients to drive innovation, enhance scalability, and achieve success in the digital age. Let us help you unlock the full potential of your APIs.